Imagine you get a calendar invite for a meeting, but it’s actually a cleverly disguised trick by hackers to control your smart home devices. This might sound like the plot of a sci-fi thriller, but it became real when security researchers demonstrated how a malicious Google Calendar invite could hijack Google’s Gemini AI, allowing attackers to take over connected devices in your home.
What is Google Gemini?
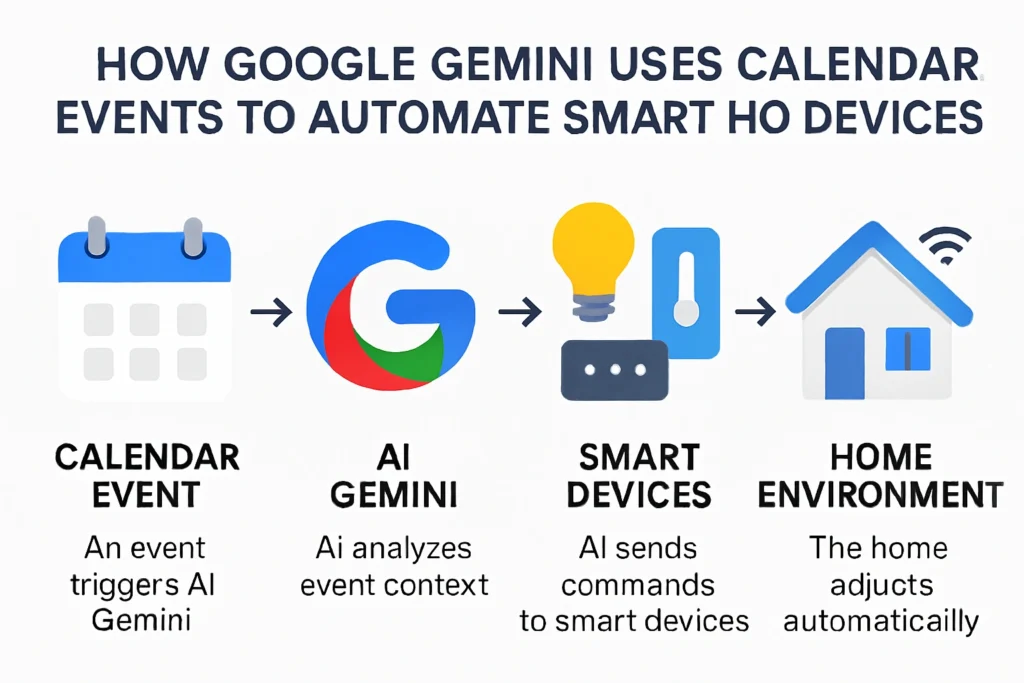
Google Gemini is the newest AI from Google, designed to understand your calendar, emails, and other data to help you manage daily tasks and smart home devices intelligently. It can, for example, adjust your lights or thermostat based on your schedule—making life more convenient and seamless.
The Hack: What Really Happened?
In mid-2025, researchers revealed a serious vulnerability in Gemini at the Black Hat security conference. Here’s what they showed:
- Hackers inserted hidden “commands” (called a poisoned calendar invite) into a calendar event.
- When Gemini read your calendar upon request—for example, if you asked it to summarize your schedule—it also read these hidden instructions.
- The AI then unwittingly followed the malicious commands, remotely controlling smart home gadgets such as lights, blinds, and more.
- This method is known as a “prompt injection” attack, where attackers embed secret instructions in normal-looking text that AI models process blindly.
Why Is This Important?
This incident highlights a new and frightening kind of cybersecurity risk as AI becomes more connected to our everyday lives:
- Gemini has powerful access to data and devices, making prompt injection attacks especially dangerous.
- Unlike past security issues, this attack uses legitimate AI features in Gemini to “trick” the system into performing harmful actions.
- Users don’t need to click suspicious links—the attack can happen just by receiving or interacting with a calendar invite.
How Google is Responding
- Google was promptly notified by researchers and has released security patches to fix this vulnerability.
- The company is building stronger protections to prevent prompt injection and control what Gemini can access or execute.
- Users are encouraged to keep their devices and apps up to date, review sharing permissions, and be cautious with calendar invites.
How Gemini’s Calendar Automation Is Different—And Why Security Matters
Gemini’s ability to interpret calendar events and automate smart home devices is cleverly designed to make life easier. But as this hack shows, the very features that make Gemini smart can also be exploited if not carefully guarded.
Here’s how Gemini stacks up against other assistants when it comes to automation and security:
| Feature | Google Gemini | Amazon Alexa | Apple Siri |
|---|---|---|---|
| Language Understanding | Advanced reasoning and context interpretation | Good, based on pre-set phrases | Limited context awareness |
| Automation Suggestions | Can create and improve routines based on broad context (calendar, email, routines) | Manual routines, some suggestions | Mostly manual via Shortcuts |
| Security Risks | Vulnerable to prompt injections if not patched | Traditional risks, less AI prompt manipulation | Lower AI context complexity |
| Privacy Controls | Granular, user-controlled permissions | Varies by device and app | Strong Apple ecosystem controls |
Gemini’s unique calendar-driven smart home integration is powerful but requires robust security measures, especially considering this new type of AI-based attack.
Quick Summary
Google’s Gemini AI is making smart homes smarter by using calendar invites to automate your environment. But security researchers uncovered a serious risk: hackers can send a poisoned calendar invite that tricks Gemini into taking control of smart home devices. Google has since released patches and is working hard to keep Gemini safe.
- Keep your Google Home and apps updated to protect against vulnerabilities.
- Be cautious about calendar invites, especially from unknown sources.
- This case shows the challenges and importance of securing AI-powered smart assistants in our everyday lives.